MSME Grant 2026
Services
Mobile App Custom mobile apps, built smart.
Software Automate tasks, simplify work, grow faster.
Software
Solutions
Web & Ecommerce Automate tasks, simplify work, grow faster.
Web Design
E-Commerce
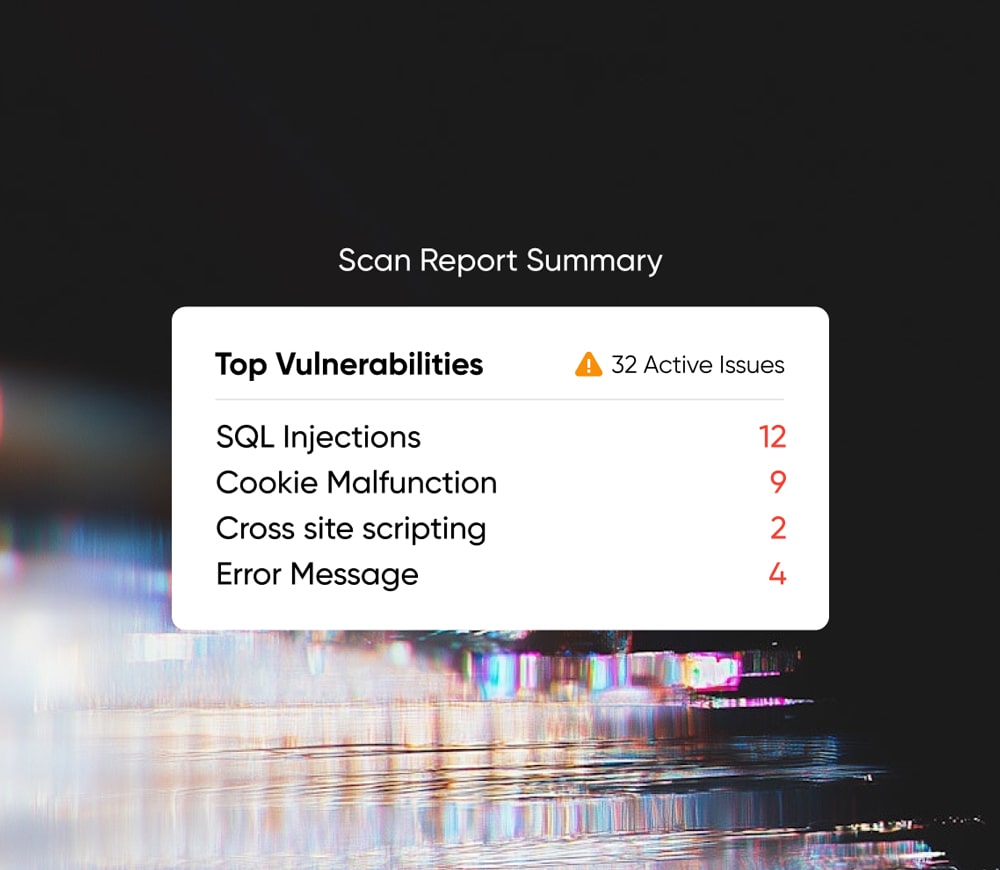
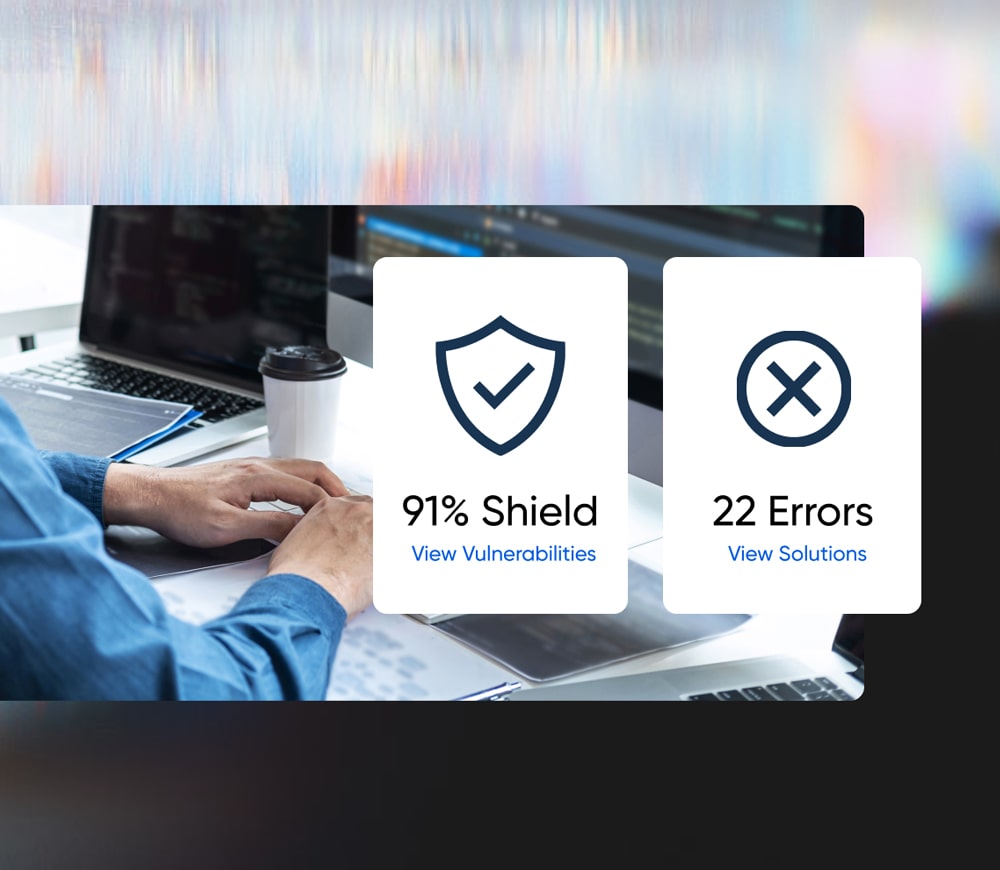
Cybersecurity Automate tasks, simplify work, grow faster.
Security Solutions
Marketing Get noticed, get leads, get growing.
Writing
Video Animation
Branding & Design
SEO & SEM Get noticed, get leads, get growing.
Organic Marketing
Paid Marketing